FinalAV Crowdsecurity Network (CSN)
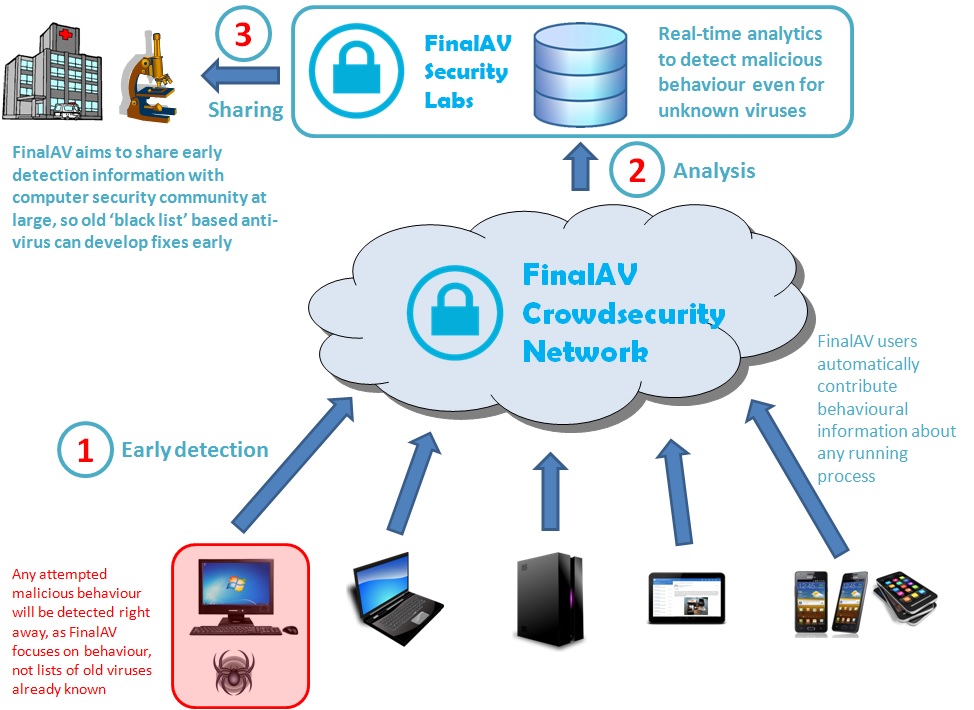
After installinng FinalAV Security in your computer system, you are not only protected against malicious activity by unidentified programs, but you are also contributing activity reports to the FinalAV Crowdsecurity Network (CSN), enabling early detection of malware. By capturing all the sensitive activities by signed and unsigned processes, FinalAV Labs will be able to detect early on any suspicious activity, even before anyone loses any data. This is the power of the community used against the cybercriminals.
Let us see an example of how this works through the lifecycle of a software virus:
1) The malware is created: a hacker intenting to steal credit card and banking password information from unsuspected victims, writes a little piece of software that silently scans the emails in a system looking for credit card details, social security numbers and online banking login information. When some information is found, this program will send a little file with the information to the hacker's servers located in a foreign jurisdiction. The hacker can later use the information to steal money from the user credit card or bank accounts, or sell the gathered information in the black market. Please see this useful report, "Markets for Cybercrime Tools and Stolen Data - Hacker's Bazaar" by RAND National Security and Research Division if you want to know more about the frightening underground cyberfraud market.
Note that to achieve its malicious goals this silent piece of software needs to be able to perform two important actions:
i) Send data (its 'bounty') to foreign unidentified servers (unidentified so they cannot be traced, otherwise the police would find them very quickly)
ii) copy itself into local and/or remote filesystems (e.g. USB drives, network drives) in order to spread itself; note this contagion capability enables the hacker to expand its reach beyond the victims that visit the partner website (or whatever other 'vector' the hacker has used, such as infected emails, PDF file, etc).
2) The malware is released in the wild: the hacker plants it in a partner website where people can download free games, online gaming, porn or whatever that can attract lots of customers. As a visitor downloads and installs a free game, he is also given a little "gift": the silent malware is installed in her computer, and from now on, every time she starts the machine that virus will run in the background scanning her emails and sending any credit card or banking password information to the hacker's servers located in a foreign jurisdiction.
3) A user gets infected: an unsuspected user visits the online gaming website, downloads and install the game, effectively also installing the silent malware in her computer. Note that at this point this virus is not known yet, and as it works silently it may go unnoticed for months, sometimes even years. At this point the hacker's business is working because gradually more and more stolen credit card and banking data is accumulated in his remore servers.
Current anti-virus solutions based on a blacklist of known viruses will not protect the victims. This is what is called "zero day vulnerability" because from the day the virus is released in the wild ("zero day") until it is identified by a victim or security researcher, users are not protected. Again, this could go on for weeks, months or even years. {Give an example here of a virus that took years to detect}
On the other hand, FinalAV Security is already protecting the user because the malware is obviously not digitally signed by the hacker (unless he or she wishes to go to jail), and so when the malware attempts to infect another drive by copying itself it will be stopped by FinalAV; likewise, when it attempts to send its 'bounty' to the hacker's servers in a remote jurisdiction, it will be stopped by FinalAV. Unsigned software is only allowed to connect to secure servers, whereby the destination point is legaly identified with a digital signature, and so legal liability exists.
Further, and here is where the FinalAV Crowdsecurity Network comes into play, a report of the prevented suspicious activity will be uploaded to the FinalAV servers.
4) FinalAV Crowdsecurity Network detects malware: our real-time analytics algorithms continually analyse the malicious activity data contributed by our user community. Our algorithms will pick up on this malicious activity even though it is performed silently, and our security researchers will be able to investigate further whether this is indeed a new piece of malware. If so, we will be able to make it known to the security community even before anyone has lost any data and/or money.
1) The malware is created: a hacker intenting to steal credit card and banking password information from unsuspected victims, writes a little piece of software that silently scans the emails in a system looking for credit card details, social security numbers and online banking login information. When some information is found, this program will send a little file with the information to the hacker's servers located in a foreign jurisdiction. The hacker can later use the information to steal money from the user credit card or bank accounts, or sell the gathered information in the black market. Please see this useful report, "Markets for Cybercrime Tools and Stolen Data - Hacker's Bazaar" by RAND National Security and Research Division if you want to know more about the frightening underground cyberfraud market.
Note that to achieve its malicious goals this silent piece of software needs to be able to perform two important actions:
i) Send data (its 'bounty') to foreign unidentified servers (unidentified so they cannot be traced, otherwise the police would find them very quickly)
ii) copy itself into local and/or remote filesystems (e.g. USB drives, network drives) in order to spread itself; note this contagion capability enables the hacker to expand its reach beyond the victims that visit the partner website (or whatever other 'vector' the hacker has used, such as infected emails, PDF file, etc).
2) The malware is released in the wild: the hacker plants it in a partner website where people can download free games, online gaming, porn or whatever that can attract lots of customers. As a visitor downloads and installs a free game, he is also given a little "gift": the silent malware is installed in her computer, and from now on, every time she starts the machine that virus will run in the background scanning her emails and sending any credit card or banking password information to the hacker's servers located in a foreign jurisdiction.
3) A user gets infected: an unsuspected user visits the online gaming website, downloads and install the game, effectively also installing the silent malware in her computer. Note that at this point this virus is not known yet, and as it works silently it may go unnoticed for months, sometimes even years. At this point the hacker's business is working because gradually more and more stolen credit card and banking data is accumulated in his remore servers.
Current anti-virus solutions based on a blacklist of known viruses will not protect the victims. This is what is called "zero day vulnerability" because from the day the virus is released in the wild ("zero day") until it is identified by a victim or security researcher, users are not protected. Again, this could go on for weeks, months or even years. {Give an example here of a virus that took years to detect}
On the other hand, FinalAV Security is already protecting the user because the malware is obviously not digitally signed by the hacker (unless he or she wishes to go to jail), and so when the malware attempts to infect another drive by copying itself it will be stopped by FinalAV; likewise, when it attempts to send its 'bounty' to the hacker's servers in a remote jurisdiction, it will be stopped by FinalAV. Unsigned software is only allowed to connect to secure servers, whereby the destination point is legaly identified with a digital signature, and so legal liability exists.
Further, and here is where the FinalAV Crowdsecurity Network comes into play, a report of the prevented suspicious activity will be uploaded to the FinalAV servers.
4) FinalAV Crowdsecurity Network detects malware: our real-time analytics algorithms continually analyse the malicious activity data contributed by our user community. Our algorithms will pick up on this malicious activity even though it is performed silently, and our security researchers will be able to investigate further whether this is indeed a new piece of malware. If so, we will be able to make it known to the security community even before anyone has lost any data and/or money.
Effectively we are leveraging the power of the user community to fight back cybercriminals, over time reducing the economic value of their malicious business. Preventing data capture and reducing the time it takes to detect any new virus greatly reduces the size of hacker's bounty.